
<What are the root problems?/>
The OWASP TOP 10 2025 in light of a unified framework
In this article, we will map each general security requirement to the latest OWASP TOP 10. This will be crucial for understanding the root of vulnerabilities, which is necessary for identifying comprehensive solutions.
The context
As we discussed in the previous article, web applications are nowadays the de facto standard underlying modern communications across the network of networks — Internet. Nowadays, they are used not only for websites—like the one you're interacting with right now—but for any type of service delivered over the Internet. These are sophisticated distributed programs that typically execute operations partly on web servers and partly on web clients (typically, your browser).
The complexity and distributed nature of web applications exposes them to countless (often subtle) vulnerabilities, making their security very difficult to address and manage. This is compounded by the popularity and widespread public availability of web applications (as well as vulnerabilities and programs to exploit them, known as exploits), which makes them a highly attractive target for cybercriminals, with low risk (the attacker's identity is difficult to trace) compared to the benefits (typically financial, but also geopolitical, etc.) associated with the exploits.
For example, cybercriminals can conveniently exploit vulnerabilities remotely and almost anonymously, potentially accessing the data of thousands, if not millions, of users to resell them on the illegal market (e.g., the dark web), or even ask for a ransom to allow data access (as in so-called ransomware). Web application security has now become a strategic and survival issue for professionals, companies of all sizes, and governments around the world. It has therefore mobilized significant international efforts, including the Open Web Application Security Project (OWASP).
The OWASP and its TOP 10
The OWASP is undoubtedly the most important international project for web application security. It is an open-source project and has a community of thousands of people and information security experts around the world. The OWASP community contributes extensively to several subprojects. Among the most famous ones, the OWASP TOP 10 is a list of the 10 most important and widespread web security threats. It is updated approximately every four years, with the most recent version being released in 2025.
What is the OWASP TOP 10 for?
In Cybersecurity in a Nutshell, we saw that security is essentially a risk analysis and management problem. In this sense, the OWASP TOP 10 can be considered a starting point, as it focuses on the security problems that most frequently affect web applications in the real world. Indeed, experimentally, web applications are often affected by problems with common characteristics. Therefore, in the absence of other information, the OWASP TOP 10 represents a good informed guess of the most likely security threats a web application will face: it is useful as a priori information, regardless of the specific context in which the application operates.
What is the main process behind the OWASP TOP 10?
In this latest edition (2025), vulnerabilities related to over 2.8 million web applications reported voluntarily by various organizations were analyzed, generating the largest, most up-to-date and complete corpus of data on web application security. To further improve the representativeness of the study, OWASP experts also collected the opinion of the international community of computer security experts through a dedicated survey (TOP 10 Community Survey).
The analysis procedure is based on the most extensive internationally available standards for the categorization of computer security vulnerabilities:
- Common Weakness Enumeration (CWE)
- Common Vulnerabilities and Exposures (CVE)
- Common Vulnerability Scoring System (CVSS)
These standards are advanced by non-profit organizations funded by the U.S. government, most notably MITRE (CWE, CVE) and the Forum of Incident Response and Security Teams (CVSS).
In the following, we briefly present the meaning and main objectives of each of these standards, both in general and in the context of the OWASP TOP 10.
Common Weakness Enumeration (CWE)
CWEs are an inventory of common security "weaknesses" found in hardware and software, useful as a reference vocabulary for classifying, preventing, and mitigating vulnerabilities. Currently, MITRE have classified about one thousand (944) different CWEs!
Each CWE is provided with a unique numerical identifier and a detailed description of the problem, with examples, bibliographical references and typical impact on fundamental security requirements (see e.g. CWE 79).
A total of 589 different CWEs were associated with the data collected by OWASP (a significant increase from the previous edition in 2021, with 400 CWEs, and the previous one in 2017, with only 30 CWEs). The OWASP expert group then selected 248 of these CWEs and grouped them into 12 categories. Only 10 of these were then selected based on the TOP 10 Community Survey.
Common Vulnerabilities and Exposures (CVE)
While CWEs are a general catalog of vulnerabilities, CVEs are very specific security vulnerabilities, which also indicate the associated vulnerable systems, where possible, with their specific version, as well as the severity of a vulnerability via the CVSS score (described briefly below). This is a highly operational catalog, which can allow for the automatic identification of vulnerable systems (via the Common Platform Enumeration (CPE) identifier) for patching, protection, and mitigation actions. Each CVE can be associated with one or more CWEs, and vice versa.
For example, you can take a look at the details of the high/critical risk CVE-2026-3061 that recently affected the Google Chrome browser.
As part of the OWASP TOP 10 analysis, the CVEs associated with the collected data (and in particular with each CWE) were used to evaluate the ease of exploitation and the technical impact of the vulnerabilities.
Common Vulnerability Scoring System (CVSS)
The CVSS standard (currently in version 4.0) was created to indicate the severity of a vulnerability through a numerical value, taking into account various parameters , such as the methods, ease, and security impact associated with exploiting a vulnerability. The numerical score can then be translated into a qualitative representation (low, medium, high, and critical severity) to help organizations correctly assess and prioritize vulnerability management.
Understanding the Root Vulnerabilities of the OWASP TOP 10
The OWASP Top 10 categories have changed significantly over time, not only based on the evidence gathered, but also and above all depending on the OWASP community's ability to identify common patterns related to the issues. The framework provided in Cybersecurity in a Nutshell provides a unique, much more stable and inclusive perspective for characterizing these phenomena.
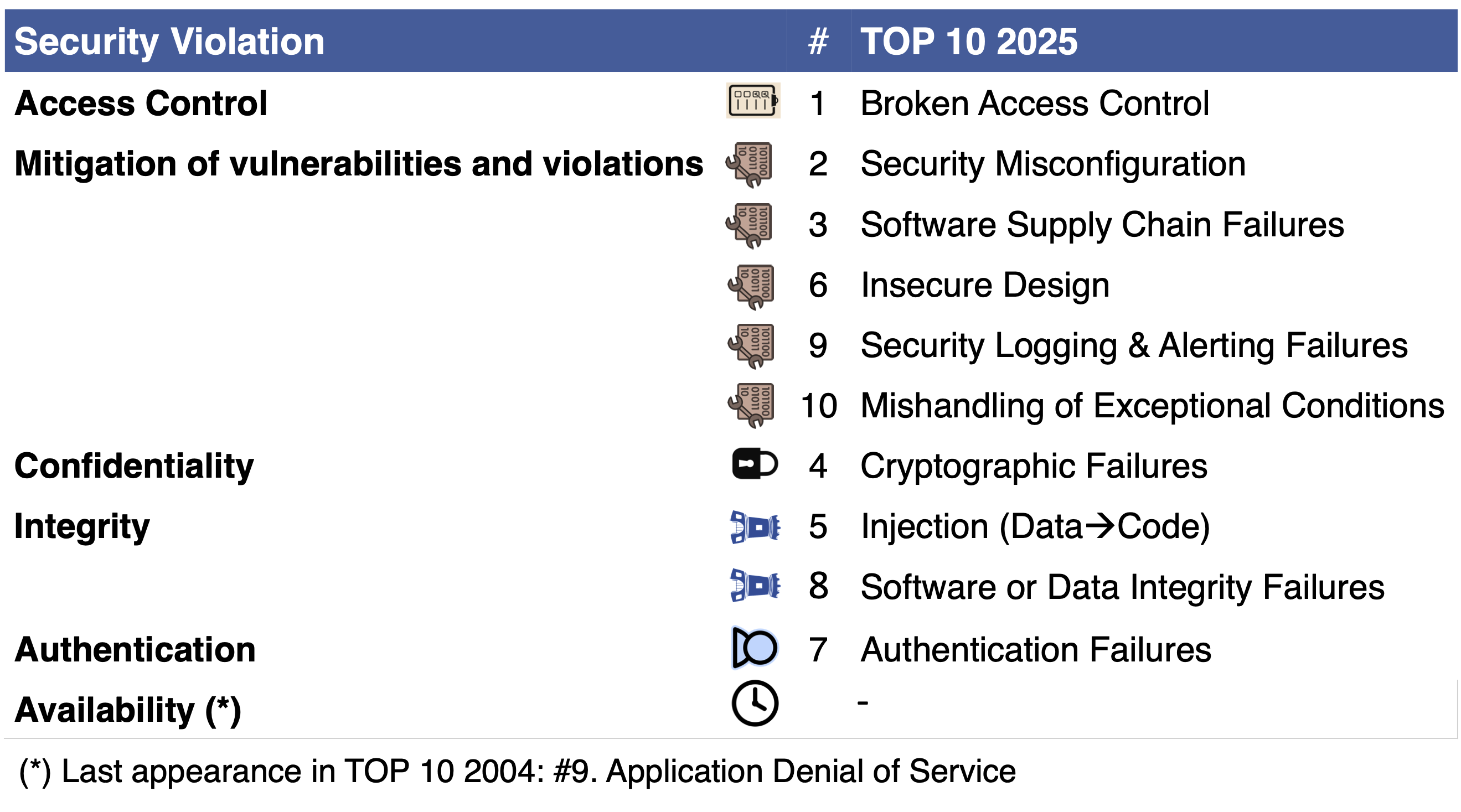
In Figure 1, for each violation of the security requirements (fundamental, functional and process) we can find a correspondence with the OWASP TOP 10 2025 macro categories.
First of all, it is interesting to note how some threats have a one-to-one correspondence with security requirements (namely, Access Control, Confidentiality and Authentication).
Access control appears to be the most problematic (Broken Access Control). The second place pertains to the macro-process requirement for mitigating vulnerabilities and violations, which can be associated with as many as 5 categories in the TOP 10:
- Incorrect or insufficient security configurations (Security Misconfiguration)
- Supply Chain Failures: Third-Party Software Components (Software Supply Chain Failures)
- System design that does not properly encompass security requirements (Insecure Design)
- Tracking and reporting of security-relevant events (Security Logging & Alerting Failures)
- Improper handling of exceptions and errors (Mishandling of Exceptional Conditions)
Confidentiality violations rank third. In this case, however, the TOP 10 2025 focuses only on a particular implementation aspect (Cryptographic Failures).
In the fourth place we find Integrity violations, which can be associated with two macro threat categories:
- Injection, which is actually an instance of more general attacks --I call them Data→Code attacks-- where data is erroneously interpreted as code by one or more software interpreters;
- generic data and software integrity violations (Software or Data Integrity Failures).
In the fifth place, we find Authentication problems, with the macro-category Authentication Failures.
Finally, it is worth noting that the Availability requirement is not included at all in the OWASP TOP 10 2025! To be precise, it hasn't been included since 2004, when it appeared in ninth place. However, Availability is undoubtedly a fundamental requirement for any application. Without adequate measures to ensure it, the related business can collapse at any moment. Attacks that violate this requirement are the so-called Denial of Service (DoS) attacks, which, when executed simultaneously by multiple systems across the Internet, are often referred to as Distributed DoS (DDoS).
In future articles, we'll delve deeper into each of the security requirements and highlight the best methods for ensuring they're met, discussing the associated OWASP TOP 10 threat macrocategories. We'll see that the Integrity requirement is among the most frequently violated by cyberattacks, allowing us to group together a multitude of attacks (well beyond the OWASP TOP 10) that only seemingly have little in common, allowing us to predict new instances and variants.
In the meantime, I hope that you now better understand the main web application security issues, how they've been analyzed by the international community, and how they can be more clearly contextualized using our general framework.
Until next time!
Find more blog posts with similar tags
